In today’s digital age, cybersecurity threats are more prevalent than ever. From phishing attacks to data breaches, organizations face constant risks that could jeopardize sensitive information. While many companies have strict cybersecurity policies in place, it’s not enough to rely solely on security software and protocols. Employees must also understand and follow best practices to mitigate these threats. This is where cybersecurity compliance training comes into play.
However, it’s not enough to merely tell employees about cybersecurity risks — training needs to be practical, engaging, and applicable to real-life scenarios. In this post, we’ll explore the key elements employees need to know and how businesses can provide effective cybersecurity compliance training.
1. Understanding the Basics of Cybersecurity Compliance
The first step in cybersecurity compliance training is ensuring employees understand the core concepts of cybersecurity. This includes an overview of how cyberattacks work, the types of threats that exist, and why safeguarding data is so critical.
Training should cover topics like:
- Password Management: Employees should learn the importance of strong passwords, how to create secure ones, and why reusing passwords across platforms is dangerous.
- Phishing and Social Engineering: One of the most common cyberattack tactics is phishing. Employees need to know how to identify phishing emails, suspicious links, and other attempts to trick them into revealing sensitive information.
- Data Protection and Encryption: Employees should understand how encryption works and how they can protect sensitive data (both personally identifiable information and company data).
The goal is to ensure employees not only recognize the significance of cybersecurity compliance but also understand their role in safeguarding the organization’s digital assets.
2. Making Cybersecurity Training Relatable with Real-World Scenarios
To make the training more effective, it’s essential to go beyond abstract concepts and introduce real-life scenarios that employees can relate to. For example:
- Phishing Simulations: Employees can be presented with examples of phishing emails (or even participate in simulated phishing exercises). By seeing what these attempts look like, employees can learn how to identify and avoid them in their inboxes.
- Scenario-Based Training: Create interactive training modules where employees make decisions based on common cybersecurity situations. For instance, what should they do if they receive an urgent email asking for sensitive information or if they suspect their computer is infected?
This type of scenario-based training enables employees to actively engage with the material and apply their learning to realistic situations they might face daily. By practicing real-world scenarios, they can feel more confident in their ability to respond appropriately when confronted with a potential threat.
3. Data Security: Employees as the First Line of Defense
One of the most important aspects of cybersecurity compliance is ensuring employees understand their role in protecting company data. This involves:
- Safeguarding Personal Devices: Many employees work from home or on the go. Ensuring that personal devices used for work are secure is essential. Employees should be trained on using Virtual Private Networks (VPNs), securing Wi-Fi networks, and avoiding unsecured public networks.
- Proper Handling of Sensitive Data: Employees must learn how to handle sensitive data safely, both online and offline. They should be trained to follow specific protocols when handling, storing, or sharing sensitive information, and understand how improper handling can lead to breaches or data leaks.
- Device Management: Employees need to be aware of the risks associated with using unauthorized devices for work tasks and the importance of updating software regularly to mitigate vulnerabilities.
Cybersecurity is not just the responsibility of IT departments; every employee plays a role in maintaining the company’s digital security.
4. Keeping Training Relevant with Regular Updates
Cybersecurity threats evolve constantly, so training needs to be an ongoing process. Organizations should update their cybersecurity training regularly to reflect the latest threats and best practices.
- Monthly or Quarterly Refresher Courses: Instead of relying on annual training sessions, companies can offer periodic updates or quick refreshers to keep cybersecurity top of mind for employees. These updates can cover new types of threats, tools, and tactics.
- New Threats and Vulnerabilities: As new types of cyberattacks emerge, such as ransomware or advanced social engineering attacks, employees need to be kept informed about how to recognize and protect against these risks.
By keeping cybersecurity training relevant, you help employees stay sharp and aware of the latest threats, ensuring the entire organization is well-prepared.
5. The Importance of a Cybersecurity Culture
Building a strong cybersecurity culture within an organization is just as important as having a solid policy in place. Employees should feel empowered to report suspicious activities without fear of repercussions.
- Open Communication: Encourage a culture where employees feel comfortable reporting any cybersecurity concerns. This might include notifying IT about potential phishing emails or suspicious website behavior.
- Leadership and Role Models: Company leaders should set the tone by following cybersecurity best practices themselves and advocating for a culture of security. If employees see leadership prioritizing cybersecurity, they are more likely to follow suit.
- Rewarding Compliance: Acknowledge employees who actively contribute to a safe and secure working environment, whether through completing additional training or spotting potential threats. Positive reinforcement can encourage others to adopt secure behaviors.
6. Ensuring Cybersecurity Compliance with Monitoring and Feedback
After the training is complete, it’s crucial to monitor and evaluate its effectiveness. Tracking completion rates, assessing quiz results, and even conducting occasional follow-up surveys or tests can help ensure that employees have absorbed the necessary knowledge.
- Regular Cybersecurity Audits: Regular assessments can help identify areas where employees might need more training or where the organization’s cybersecurity protocols could be strengthened.
- Real-Time Feedback: Employees should receive feedback on their actions during training exercises (e.g., phishing tests or incident response simulations). Immediate feedback helps them recognize areas where they can improve and reinforces the correct actions.
Conclusion: Protecting Your Organization Starts with Employee Awareness
Cybersecurity compliance training is no longer optional. As the first line of defense, employees need to understand how their actions can impact an organization’s digital security. By making training relevant, interactive, and ongoing, businesses can empower their employees to recognize threats, respond effectively, and contribute to a robust cybersecurity culture.
In today’s rapidly evolving digital landscape, ensuring that employees are well-equipped to navigate and mitigate cyber risks is essential. When everyone is trained and aware, the organization becomes significantly stronger in protecting its data and assets against cyber threats.
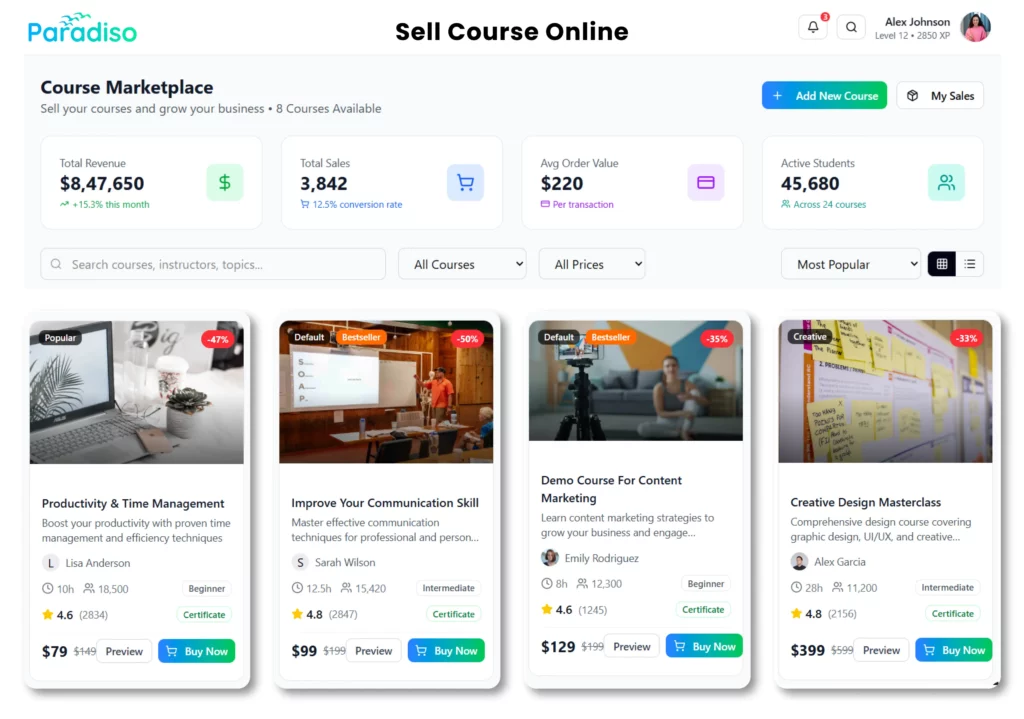
To learn more about how to implement effective cybersecurity compliance training, visit Paradiso’s Compliance Training Platform.
 Skip to content
Skip to content